Telegram is no longer just a messaging app. It has become the front line for breaking news, conflict reporting, and investigative journalism. But it is also a minefield of unverified claims, deepfakes, and coordinated disinformation campaigns. For journalists and researchers, the challenge isn't finding information-it's finding original evidence that can stand up to scrutiny. You cannot simply screenshot a post and publish it. You must prove the source, verify the context, and ensure the content hasn't been manipulated or taken out of sequence.
This guide breaks down the practical steps for sourcing authentic evidence from Telegram, drawing on methodologies used by organizations like the Organized Crime and Corruption Reporting Project (OCCRP) and academic datasets like TGDataset. Whether you are tracking geopolitical conflicts or investigating local corruption, these verification standards will help you separate signal from noise.
Understanding the Telegram Ecosystem for Evidence
To source evidence effectively, you first need to understand where you are looking. Unlike platforms with heavy algorithmic curation or strict moderation, Telegram operates as a largely unmoderated public square. As of recent academic analyses, there are over 120,000 documented public channels containing hundreds of millions of messages. This volume creates both opportunity and risk.
The platform’s structure favors speed over accuracy. Channels often act as amplifiers rather than originators. Research published in the Journal of Information Technology and Politics found that links to misleading sources are shared significantly more frequently than links to professional news outlets. However, this doesn't mean the entire platform is unreliable. The same research revealed that misinformation is concentrated in small, active communities rather than spread broadly across all users. Your job is to identify those specific clusters and avoid them, or document them carefully if they are part of your story.
- Public Channels: These are searchable and visible to anyone. They are the primary source for OSINT (Open-Source Intelligence). Look for channels with consistent posting histories and transparent ownership.
- Private Groups: Access requires an invite link. Evidence from here is harder to obtain but often contains raw, unfiltered data from insiders or participants.
- Bots and Bots Networks: Automated accounts that repost content. Be wary of channels that rely heavily on bots, as they often lack human verification.
Step-by-Step: Extracting and Preserving Digital Evidence
You cannot rely on screenshots alone. Screenshots are easily fabricated and lack metadata. To build a defensible case, you need to export the raw data. This process transforms ephemeral messages into structured, analyzable files.
- Export Data via Desktop App: Use Telegram Desktop to export chat history. Select the specific channel or group. Choose JSON format for text data, and ensure you check boxes for photos, videos, and audio files. This creates a folder structure with all media and a
messages.jsonfile containing timestamps, user IDs, and forwarding chains. - Use Forensic Tools: Platforms like Paliscope Explore allow you to import these JSON exports directly. These tools help organize large datasets, enabling you to search across thousands of messages using Boolean operators. They also support visual searches, allowing you to find specific objects or locations within video frames.
- Preserve Metadata: Never strip metadata from images or videos before analysis. Exif data can reveal camera models, GPS coordinates, and exact timestamps. If the metadata is missing, note this in your report as a potential red flag for manipulation.
Once exported, treat the data as sensitive. Store it securely, preferably encrypted, and maintain a chain of custody log documenting who accessed the files and when. This is crucial if your findings are challenged legally or ethically.

Verifying Authenticity: Cross-Referencing and Geolocation
Having the file is only half the battle. You must verify what it shows. A video of a burning building means nothing without context. Is it from today? Is it from the location claimed? Or is it footage from a conflict five years ago?
Start with reverse image and video searches. Upload key frames to tools like Google Reverse Image Search, Yandex Images, or specialized OSINT tools like TinEye. This helps identify if the media has appeared online previously under different contexts. If you find matches, trace the earliest known appearance. This establishes the timeline and original source.
Next, perform geolocation. Analyze visual clues in the footage: street signs, architecture, power lines, vegetation, and even shadows. Compare these against satellite imagery from Google Earth or Mapillary. Pay attention to unique landmarks. If a channel claims a video was filmed in City X, but the street layout matches City Y, you have grounds to dispute the claim. Document your geolocation process with screenshots and maps to show your work.
Audio verification is equally important. Many Telegram posts include voice messages or background audio. Transcribe the audio using AI tools, then analyze the language and dialect. Does the accent match the region claimed? Are there background noises (air raid sirens, specific traffic sounds) that align with the alleged time and place? Audio fingerprints can also be checked against databases of known recordings.
Identifying Misinformation and Coordinated Campaigns
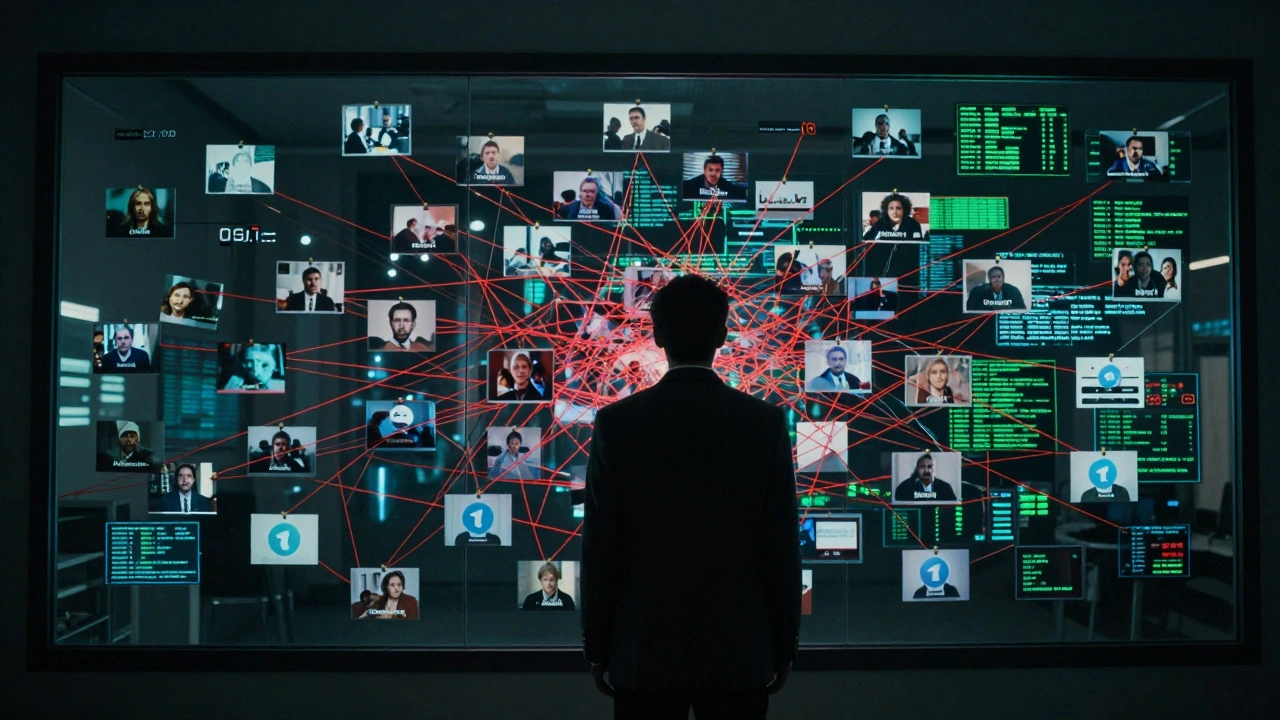
Not all false information is accidental. Some is deliberate, coordinated, and funded. Understanding the profit models behind Telegram channels helps you spot inauthentic behavior. Many conspiracy and propaganda channels actively seek to monetize their subscribers through ads, affiliate links, or donations. This financial incentive drives sensationalism and fabrication.
Academic research, such as the "Conspiracy Money Machine" study, identified thousands of URLs linking to conspiracy-related content on Telegram. The methodology involved graph analysis to map connections between channels. If multiple channels share identical posts at the same time, use the same stock photos, or employ similar bot-like posting patterns, you are likely looking at a coordinated network.
| Indicator | Description | Action |
|---|---|---|
| Synchronized Posting | Multiple channels post identical content within minutes of each other. | Flag as potential bot network; verify original source. |
| Generic Profile Pictures | Channels use default avatars or low-quality, unrelated images. | Lower credibility score; seek alternative sources. |
| Lack of Historical Context | Channel created recently but claims long-term expertise or insider access. | Investigate creation date; cross-check claims with older records. |
| Monetization Links | Frequent links to crypto wallets, donation pages, or affiliate products. | Assess bias; content may be designed to drive engagement for profit. |
When you suspect coordination, do not dismiss the content outright. Instead, document the pattern. Explain in your reporting how the narrative is being amplified artificially. This adds depth to your analysis and warns readers about the manipulative tactics at play.
Best Practices for Journalistic Integrity
Sourcing from Telegram requires a high degree of transparency. Readers need to know exactly how you verified your claims. Here are essential practices to follow:
- Triangulate Sources: Never rely on a single Telegram post. Corroborate claims with independent sources: eyewitnesses on the ground, official statements, satellite imagery, or reports from other reputable news outlets.
- Distinguish Forwarded Content: Telegram allows users to forward messages. Always check if a post is original or forwarded. If forwarded, trace back to the original sender. The original source may have higher credibility than the amplifier.
- Contextualize Time and Place: Clearly state when and where the evidence was gathered. If the timing is uncertain, say so. Ambiguity should be acknowledged, not hidden.
- Avoid Doxing: Protect the privacy of individuals unless their identity is publicly relevant and safe to disclose. Mask faces in videos and blur license plates unless necessary for the story.
- Update Corrections Promptly: If new evidence disproves an earlier claim, correct it immediately and visibly. Transparency builds trust.
Remember, your goal is not just to report what happened, but to explain how you know it happened. This methodological rigor is what separates professional journalism from rumor-mongering.
Tools and Resources for Verification
You don't have to do this manually. Several tools streamline the verification process:
- Paliscope Explore: Ideal for importing and analyzing large Telegram datasets. Supports visual and textual searches.
- Flashpoint: Provides OSINT intelligence specifically tailored for threat actors and fraud investigations.
- TGDataset: An academic resource containing metadata from over 120,000 public Telegram channels. Useful for understanding channel networks and propagation patterns.
- InVID Plugin: A browser extension for verifying video authenticity. Helps detect manipulation and extract keyframes for reverse searching.
- Geoguessr / Mapillary: Assist in geolocation by providing street-level imagery and geographic quizzes to train your eye for visual clues.
Familiarize yourself with these tools before a crisis hits. When breaking news unfolds, you won't have time to learn software. Practice exporting data, running searches, and mapping locations during quieter periods.
Can I use screenshots from Telegram as evidence in court?
Screenshots alone are rarely admissible because they can be easily forged. Courts typically require authenticated digital exports, including metadata, hash values, and a clear chain of custody. Always export full chat histories in JSON format and preserve original media files with their Exif data intact.
How do I verify if a Telegram channel is legitimate?
Check the channel's creation date, posting consistency, and engagement patterns. Legitimate channels usually have a history of diverse content and genuine interaction. Be skeptical of channels created recently that post identical content simultaneously with others, as this suggests bot activity or coordinated manipulation.
What is the best way to handle anonymous tips from Telegram?
Treat anonymous tips as leads, not facts. Verify every claim through independent sources. Ask for additional evidence, such as documents or videos, and cross-reference them with public records. Protect the tipster's identity by using secure communication methods and avoiding any details that could reveal their location or identity.
Is it legal to scrape data from public Telegram channels?
Legality varies by jurisdiction. In many places, scraping publicly available data is permissible for journalistic or research purposes, provided you comply with terms of service and privacy laws. Always consult legal counsel before conducting large-scale data collection, especially if involving personal data of individuals.
How can I detect deepfakes in Telegram videos?
Look for inconsistencies in lighting, facial expressions, and lip synchronization. Use AI detection tools like Microsoft Video Authenticator or Intel's FakeCatcher. Reverse image search key frames to see if the person appears in other contexts. Deepfakes often fail under close scrutiny of natural movements and environmental reflections.