Imagine a scenario where a whistleblower's identity or a month's worth of investigative research vanishes into a cybercriminal's database because of a single click. For many modern newsrooms, Telegram is the go-to for fast communication and sourcing. But here is the hard truth: using it as a secure vault for sensitive data is a dangerous gamble. While it feels private, the platform is simultaneously the primary marketplace for the cybercrime economy, where stolen credentials and "stealer logs" are traded in real-time.
The Hidden Risks of Telegram's Architecture
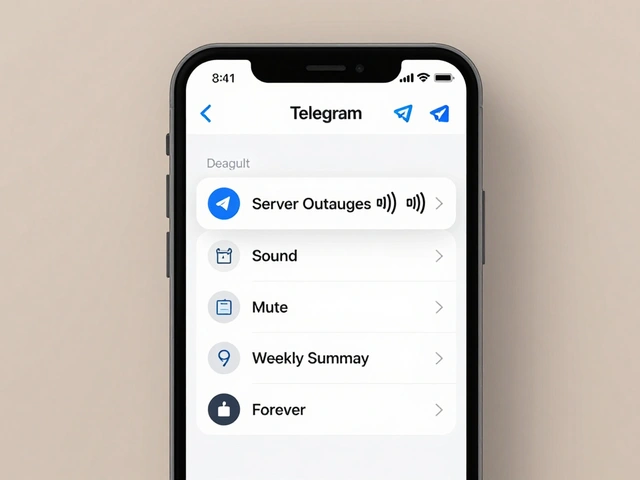
Most journalists assume that if a chat is encrypted, it's safe. However, Telegram is a cloud-based instant messaging service that does not use end-to-end encryption by default for group chats and channels . This is a massive blind spot for newsrooms. If you're coordinating a story in a group chat, that data lives on Telegram's servers in a readable format. Only "Secret Chats"-which must be started manually and only work for one-on-one conversations-offer true end-to-end encryption.
The technical backbone of the app relies on MTProto is a custom cryptographic protocol developed by Telegram to handle its encryption and data transmission . Unlike industry-standard protocols, MTProto has been flagged by security researchers for having vulnerabilities. This means that theoretically, a sophisticated attacker or an insider with server access could intercept and read your non-secret correspondence. When you combine this with the fact that governments can issue subpoenas under the Stored Communications Act to access stored records, the "privacy" of a newsroom channel becomes very fragile.
The One-Click IP Leak Trap
For journalists working in restrictive environments, the built-in proxy system seems like a lifesaver. But there is a critical flaw in the MTProxy is a proxy protocol used by Telegram to help users bypass censorship and connect to the service in blocked regions system. When you click a proxy configuration link (like t.me/proxy?...), the app performs a connectivity check to see if the server is online.
The problem? This check happens in the background before you confirm anything, and it routes directly through your real network interface. It completely ignores any VPN or SOCKS5 proxy you have running. In an instant, your real IP address is leaked to whoever owns that proxy server. For a source trying to remain anonymous, this one mistake can lead them straight to a government agency or a hostile actor.
| Feature | Cloud Chats / Groups | Secret Chats |
|---|---|---|
| Encryption Type | Server-Client (Stored on Cloud) | End-to-End (Device-to-Device) |
| Availability | All chats, groups, and channels | One-on-one only |
| Server Access | Telegram can theoretically read data | Only participants can read data |
| Device Sync | Syncs across all devices | Tied to a single device |

Weaponizing the Stealer Log Economy
Cybercriminals don't just use Telegram for chatting; they use it as a distribution hub for Stealer Logs is datasets containing usernames, passwords, and browser cookies harvested from infected devices via malware . In 2024, datasets appearing in gated Telegram communities exposed hundreds of millions of unique email addresses. If a journalist uses the same password for their Telegram account as they do for their email or CMS, a single "infostealer" infection on their laptop can compromise their entire identity.
These logs are often shared in "gated communities"-private groups where access is bought or earned. Because these are hidden from public view, newsroom security teams can't easily monitor if their organization's credentials have been leaked. By the time a breach is noticed, the attacker has usually already pivoted from the compromised account into the newsroom's internal network.
Essential Defensive Measures for Newsrooms
You don't have to abandon the platform entirely, but you must treat it as a high-risk channel. Here is how to harden your newsroom's posture:
- Mandate Multi-Factor Authentication (MFA): This is your most powerful defense. Even if your password leaks in a Telegram combo-list, MFA prevents an attacker from hijacking your account. Use a strong, unique password that is not reused anywhere else.
- Switch to Device-Level VPNs: Stop relying on Telegram's internal proxies. A system-wide VPN is a virtual private network that creates an encrypted tunnel for all internet traffic leaving a device ensures that even background connectivity checks are masked, preventing the IP leaks associated with MTProxy.
- Audit Active Sessions: Make it a habit to check the "Devices" or "Active Sessions" menu in settings. If you see a login from a city or device you don't recognize, terminate the session immediately and change your password.
- Implement SIEM Monitoring: For larger media houses, using a SIEM is Security Information and Event Management software that aggregates and analyzes log data to detect security threats allows the IT team to spot unusual API abuse or login patterns before they become full-scale breaches.
- Export and Archive Data: Since Telegram is a cloud service, you are at the mercy of their servers. Use the official desktop client (Settings > Advanced > Export Telegram data) to create local, encrypted backups of critical source communications.

Choosing the Right Tool for the Job
The biggest mistake a newsroom can make is using one tool for everything. Telegram is fantastic for broadcasting news to thousands of followers or coordinating low-stakes logistics. It is not built for high-stakes investigative journalism.
If you are dealing with confidential sources or pre-publication sensitive stories, you should move the conversation to platforms that offer true group end-to-end encryption. Signal is an open-source messaging app that provides end-to-end encryption for all communications by default is generally considered the gold standard for this. Similarly, Wire is a secure communications platform that offers encrypted messaging and calling for teams and enterprises provides a more structured environment for professional collaboration without sacrificing the encryption of group chats.
Does Telegram's secret chat protect my identity from the government?
Secret chats use end-to-end encryption, meaning the contents aren't stored on Telegram's servers. However, Telegram still collects metadata-like who you talked to and when. Under laws like the Stored Communications Act, this metadata can still be subpoenaed, and if your device is seized, the chats are accessible unless you have a strong app lock.
Why isn't a VPN enough to stop all Telegram leaks?
A VPN hides your IP address and encrypts your traffic, but it doesn't protect the data *inside* the app. If you are using a standard group chat, the data is decrypted on Telegram's servers. A VPN protects the "pipe" the data travels through, but it doesn't change where the data is stored or who has the keys to read it on the server side.
What are 'stealer logs' and how do they affect journalists?
Stealer logs are files created by malware (infostealers) that scrape passwords, cookies, and autofill data from a user's browser. These are sold in Telegram channels. If a journalist's device is infected, their Telegram credentials end up in these logs, allowing hackers to impersonate them, access their contacts, and steal sensitive editorial documents.
Can I use Telegram's proxy settings to stay anonymous?
No. As mentioned, the MTProxy system has a vulnerability where connectivity checks can bypass your VPN and leak your real IP address. For true anonymity, always use a reputable device-level VPN and avoid clicking proxy configuration links from untrusted sources.
How often should a newsroom backup their Telegram data?
At a minimum, sensitive project data should be backed up weekly. Because Telegram allows users to edit or delete messages for both parties, a source could potentially remove evidence or a critical lead. Regular exports via the desktop client ensure you have a permanent record for editorial and legal protection.
Next Steps for Your Security Team
If you are the security lead for a newsroom, start by auditing your staff's account settings. Ensure that every single account has 2FA enabled-no exceptions. Next, run a training session specifically on how to spot "stealer" phishing attempts, as these are the primary way accounts get compromised before appearing in Telegram leak channels.
Finally, create a clear Platform Policy. Categorize your communications: Use Telegram for public outreach and quick team updates, but mandate Signal or Wire for any conversation involving a confidential source or a story that could lead to legal repercussions. When the stakes are this high, convenience should never come before security.