Key Takeaways for News Teams
- High-risk items require a "Three-Point Check" before moving up the chain of command.
- Escalation should be based on risk levels (Low, Medium, High, Critical) rather than just urgency.
- Technical metadata analysis is non-negotiable for leaked documents.
- External verification from independent security firms is required for critical threats.
Defining the Risk Hierarchy
Not every "breaking" post on a Telegram channel deserves an emergency meeting. To avoid burnout and noise, newsrooms need a clear risk matrix. A low-risk item might be a rumor about a celebrity's health, while a critical-risk item is a leaked government document suggesting an imminent military action.
When an item is flagged, the desk editor must categorize it immediately. For instance, if a channel like Check Point Research flags a new wave of malware distribution through Telegram, that's a technical risk. If a political operative leaks a voice note of a world leader, that's a geopolitical risk. The escalation path differs for each. A technical risk goes to the cybersecurity lead; a geopolitical risk goes to the legal team and the editor-in-chief.
| Risk Level | Example Scenario | Verification Requirement | Final Sign-off |
|---|---|---|---|
| Low | Unverified social trend | Two independent sources | Section Editor |
| Medium | Company leak / Scandal | Document audit + Source ID | Managing Editor |
| High | Public safety threat | Cross-platform triangulation | Editor-in-Chief |
| Critical | State-sponsored disinformation | Forensic analysis + Legal review | Board / Legal Counsel |
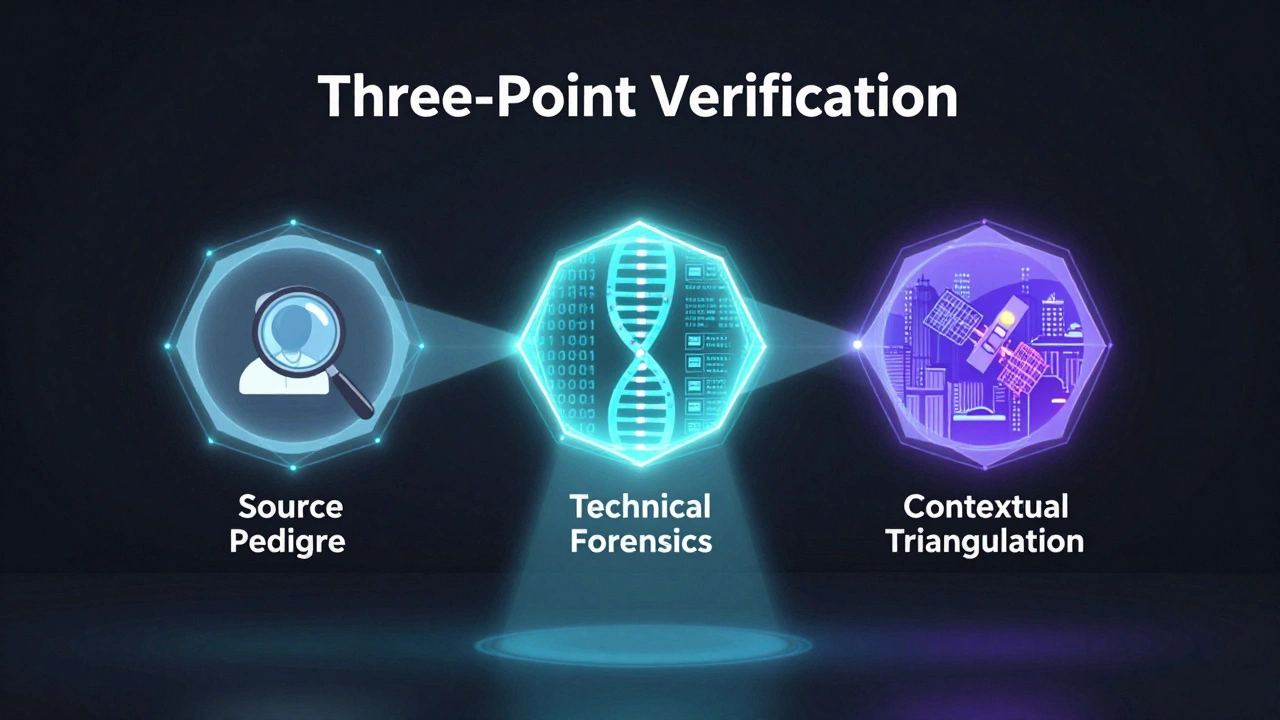
The Three-Point Verification Standard
Before a news item is escalated to the "Critical" stage, it must pass three distinct layers of scrutiny. Relying on a single "trusted" Telegram channel is a recipe for disaster, as many accounts are compromised or operated by intelligence agencies.
- Source Pedigree: Who owns the channel? Does it have a history of accuracy? We look for "lateral verification"-finding the same information in a different linguistic or regional context. If a "leak" appears only in one English-language Telegram channel but isn't being discussed in the local language of the country it concerns, it's a red flag.
- Technical Forensics: For files and images, we use Metadata Analysis. If a PDF is leaked, we check the author tags and creation dates. If a screenshot is provided, we look for compression artifacts that suggest manipulation. The FBI recently warned about Iranian actors using Telegram to distribute malware; in those cases, the "news" was actually a delivery vehicle for a payload.
- Contextual Triangulation: Does the news align with known realities? If a Telegram post claims a city has fallen, we check satellite imagery or local traffic cams. We don't just look for other news reports; we look for raw physical evidence.
Operational Escalation Workflows
Once the three-point check is complete, the item enters the escalation workflow. This isn't just about sending an email; it's about a structured hand-off of responsibility. In a high-pressure environment, a "Critical" item should trigger an immediate "War Room" call.
The flow usually looks like this: Junior Researcher → Verification Lead → Legal Counsel → Editor-in-Chief. At each step, the person receiving the information must be able to answer: "What is the cost of being wrong?" If the cost is a lawsuit or a diplomatic incident, the threshold for evidence rises.
One common pitfall is "urgency bias." This happens when a reporter convinces an editor that they must publish now to beat a competitor. To counter this, the protocol should mandate a "Cooling Period" for critical items-a forced 15-to-30 minute window where the team actively tries to disprove the story. If you can't debunk it in 30 minutes with a dedicated effort, the risk of it being true increases.

Dealing with Platform Volatility
Telegram's own internal policies change rapidly, which affects how we handle news. For example, in 2025, the platform blocked millions of channels to combat illegal content. This means a source you've relied on for months could vanish overnight. Your protocol must include a "Mirroring Strategy"-archiving high-risk items immediately using third-party tools so that the evidence isn't deleted by the platform before the legal team can review it.
We also have to account for the "Identity Pivot." Threat actors and disinformation agents often delete their channels and recreate them under new names within hours. If a high-risk news item comes from a "newly created" channel with a sudden spike in followers, the escalation protocol should automatically bump it to "High Risk" regardless of the content, as this is a classic signature of a coordinated influence operation.

Common Pitfalls in High-Risk Escalation
The biggest mistake newsrooms make is treating Telegram like a traditional wire service. It's not. Many teams fall for the "Echo Chamber Effect," where three different channels post the same leak, and the team assumes they have three independent sources. In reality, all three channels might be sharing a single press release from the same intelligence agency.
Another issue is the lack of clear "Kill Switches." A good protocol doesn't just tell you how to publish; it tells you how to retract. If a story is escalated to publication but later found to be a deepfake, there must be a pre-approved communication plan to alert the public without destroying the organization's credibility. This includes a clear statement on why the verification failed and what the new evidence shows.
How do I know if a Telegram source is reliable?
Reliability is measured by a track record of accuracy and transparency. A reliable source typically provides original documents rather than screenshots and is willing to explain their access to the information. If a source refuses to provide any identifying context or demands payment for "exclusive" high-risk news, they should be treated as high-risk and escalated for extreme scrutiny.
What is the best way to archive Telegram evidence?
Use a combination of full-page screenshots (with timestamps and URLs) and specialized archival tools that save the HTML structure of the web version of Telegram. Because channels can be deleted or messages edited, you need an immutable record that includes the channel's unique ID and the specific message ID.
How do we handle "leaked" audio or video files?
Audio and video should be sent to a forensic expert to check for AI-generated artifacts (deepfakes). We look for unnatural breathing patterns in audio or inconsistent lighting and blurring in video. No high-risk audio should be published without a spectral analysis to ensure it hasn't been spliced or manipulated.
What should we do if a source disappears during the verification process?
If a source deletes their account or channel while you are verifying, it is a major red flag. This often indicates the source was a "burn account" used for a specific operation. The protocol should be to halt escalation and treat the information as potentially hostile until independent confirmation is found.
Who should have the final say in escalating a story to publication?
For high-risk items, the final sign-off must be a joint decision between the Editor-in-Chief and Legal Counsel. The editor handles the journalistic value, while the legal counsel assesses the risk of litigation or government sanctions. Neither should be able to override the other in critical-risk scenarios.
Next Steps for Your Newsroom
If you're just starting to build these protocols, don't try to solve everything at once. Start by creating your Risk Matrix. Define exactly what constitutes a "Critical" risk for your specific beat. Then, run a "Fire Drill"-give your team a fake high-risk Telegram leak and see where the communication breaks down. Most teams find that the gap isn't in the verification, but in the hand-off between the researcher and the decision-maker.
For those in high-security environments, consider integrating a threat intelligence platform that monitors Telegram channel patterns. Knowing that a specific network of channels always "primes" the public with rumors before a fake leak drops can help you spot a campaign before it even begins.